The U.S. Federal Bureau of Investigation (FBI) warned Americans against using foreign-developed mobile […]
Improper Neutralization of Special Elements used in an SQL Command (‘SQL Injection’) vulnerability […]
This is the fifth update to the TeamPCP supply chain campaign threat intelligence […]
A new service on the cybercrime market provides automated capabilities to create persistent […]
Ravie LakshmananApr 01, 2026Social Engineering / Malware Microsoft is calling attention to a […]
Remote access and trusted administrative tools play a central role in how organizations […]
Improper Neutralization of Special Elements used in an SQL Command (‘SQL Injection’) vulnerability […]
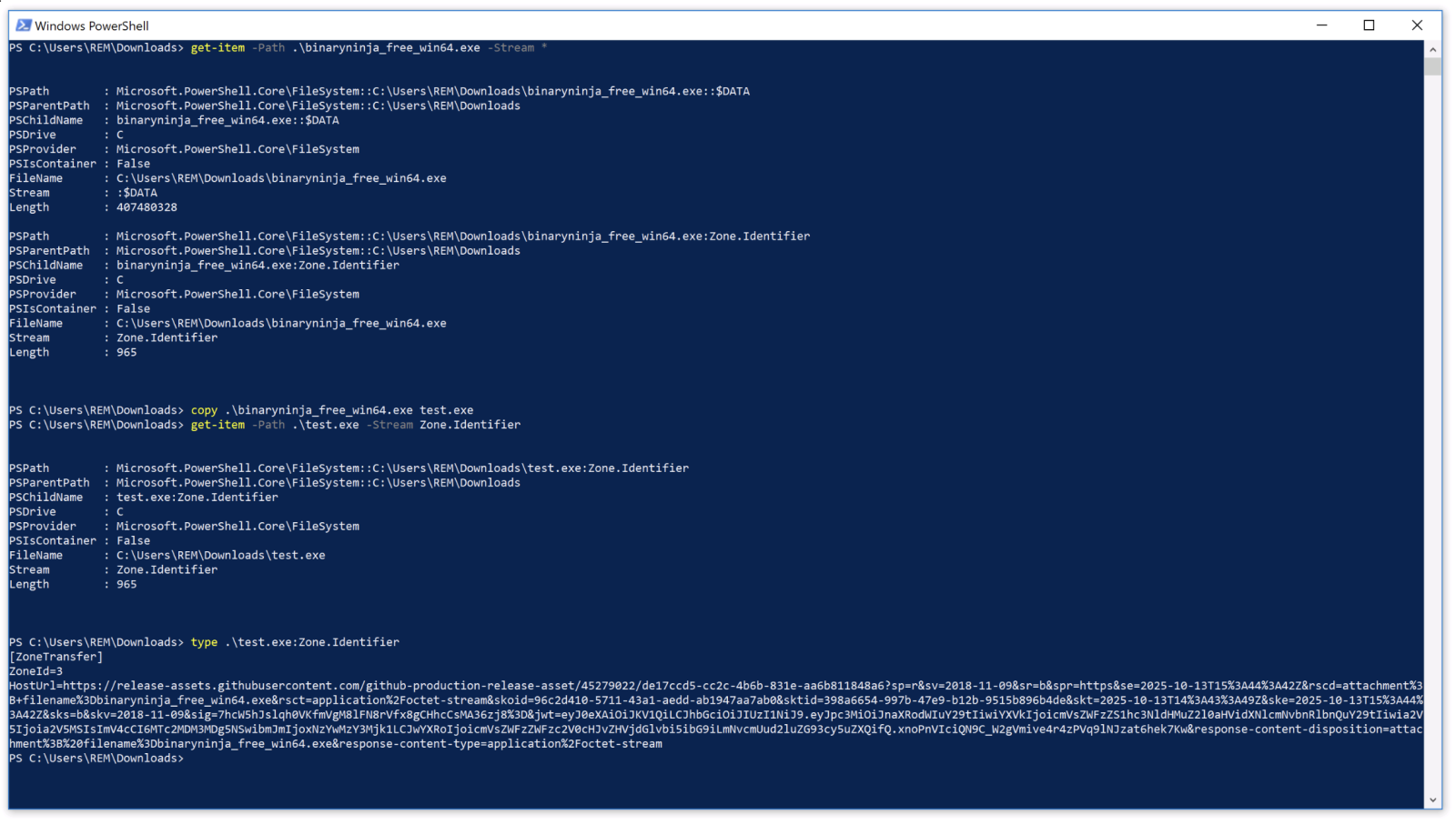
Today, most malware are called “fileless” because they try to reduce their footprint […]
Ask the Expert: Cybersecurity teams need to expand their field of view to […]
For years, cybersecurity has followed a familiar model: block malware, stop the attack. […]