Improper Neutralization of Special Elements used in an SQL Command (‘SQL Injection’) vulnerability […]
Last week, I wrote about attackers scanning for various webshells, hoping to find […]
PRT-scan is the second campaign in recent months where a threat actor appears […]
Anthropic restricted its Mythos Preview model last week after it autonomously found and […]
The MStore API plugin for WordPress is vulnerable to Unauthorized Account Access and […]
AI dominated RSAC 2026 Conference, but it’s still the humans in cybersecurity who […]
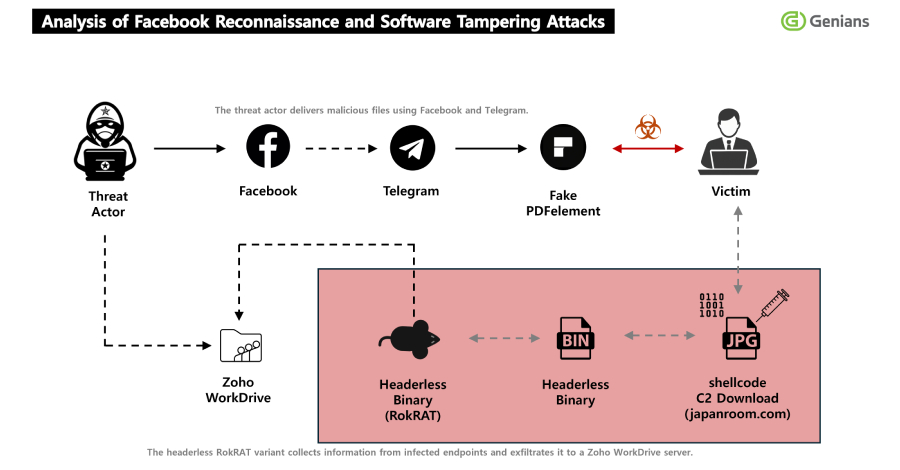
Ravie LakshmananApr 13, 2026Social Engineering / Threat Intelligence The North Korean hacking group […]
A panel of five C-suite leaders discuss how cybersecurity success is measured and […]