A 23-year-old university student in Taiwan was arrested for interfering with the TETRA […]
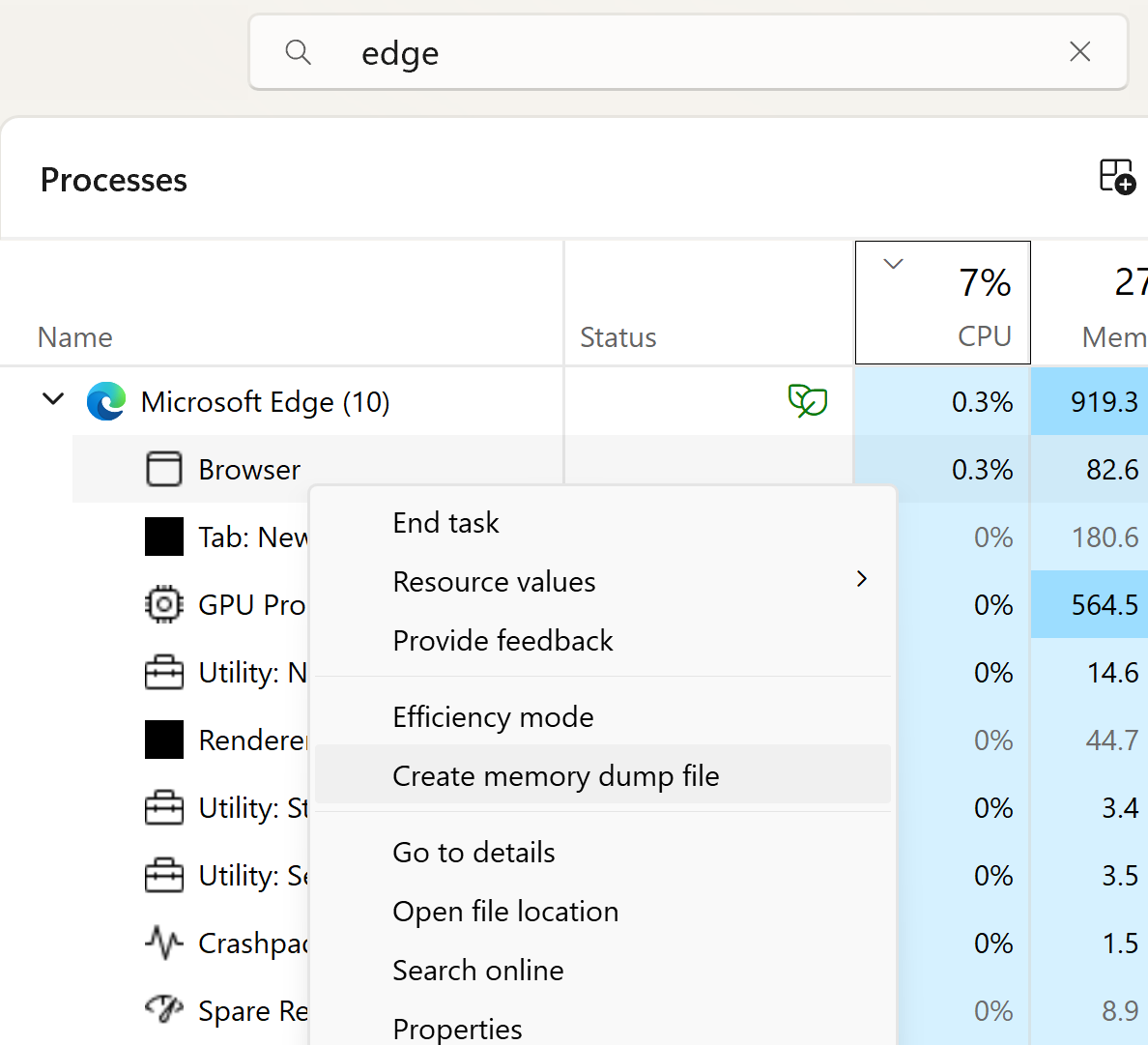
A proof-of-concept exploit (PoC) shows how someone with admin privileges can exploit the […]
Ravie LakshmananMay 05, 2026Network Security / Endpoint Security A sophisticated China-nexus advanced persistent […]
The Federal Trade Commission (FTC) will ban data broker Kochava and its subsidiary […]
WASHINGTON – Today, the Cybersecurity and Infrastructure Security Agency (CISA) released guidance to help critical infrastructure (CI) entities across all sectors prepare to operate through […]
Yup, that is for real. For me, this started with a post in […]
Two decades ago Dark Reading posted its first blockbuster — a column by […]
Every AI tool, workflow automation, and productivity app your employees connected to Google […]
The ShinyHunters extortion gang stole personal information belonging to over 119,000 people after […]
I just got an email from SSL.com last night, they are rotating out […]