Researchers find malicious repositories can trigger code execution in Claude Code with minimal […]
A 20-year-old California man was sentenced to 78 months in prison for serving […]
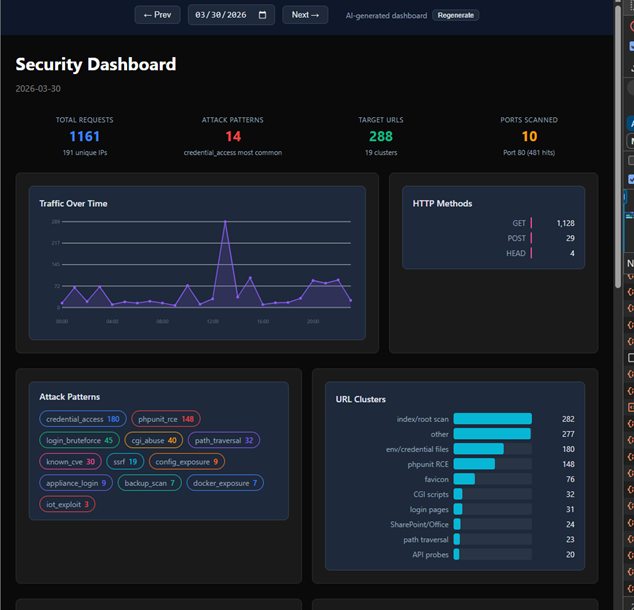
Most network incidents don’t escalate due to a lack of alerts—they escalate when […]
The MuddyWater Iranian hackers disguised their operations as a Chaos ransomware attack, relying […]
[This is a Guest Diary by Eric Roldan, an ISC intern as part […]
Disc Soft Limited, the maker of DAEMON Tools Lite, confirmed that the software […]
ISC Stormcast For Thursday, May 7th, 2026 https://isc.sans.edu/podcastdetail/9922, (Thu, May 7th) Source link […]
ShinyHunters’ attack on Instructure, which owns the widely used Canvas learning management system […]
Cisco released security updates to fix a Crosswork Network Controller (CNC) and Network […]
Authors of the VoidStealer Trojan uncovered a way to get around Google’s App-Bound […]