Ravie LakshmananMar 27, 2026Ransomware / Malware Threat actors are using adversary-in-the-middle (AitM) phishing […]
Rising geopolitical tensions are reflected (or in some cases preceded) by cyber operations, […]
Ravie LakshmananMar 27, 2026Vulnerability / Artificial Intelligence Cybersecurity researchers have disclosed three security […]
Apple is urging users who are still running an outdated version of iOS […]
Ravie LakshmananMar 26, 2026Cybersecurity / Hacking News Some weeks in security feel loud. […]
Unmasking impostors is something the art world has faced for decades, and there […]
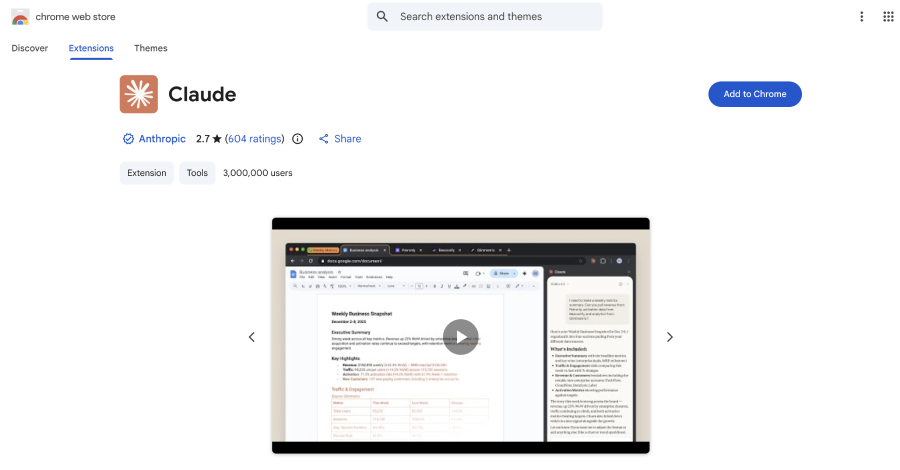
Ravie LakshmananMar 26, 2026Browser Security / Vulnerability Cybersecurity researchers have disclosed a vulnerability […]
A long-term and ongoing campaign attributed to a China-nexus threat actor has embedded […]
The Hacker NewsMar 26, 2026Security Testing / Security Automation Most teams have security […]
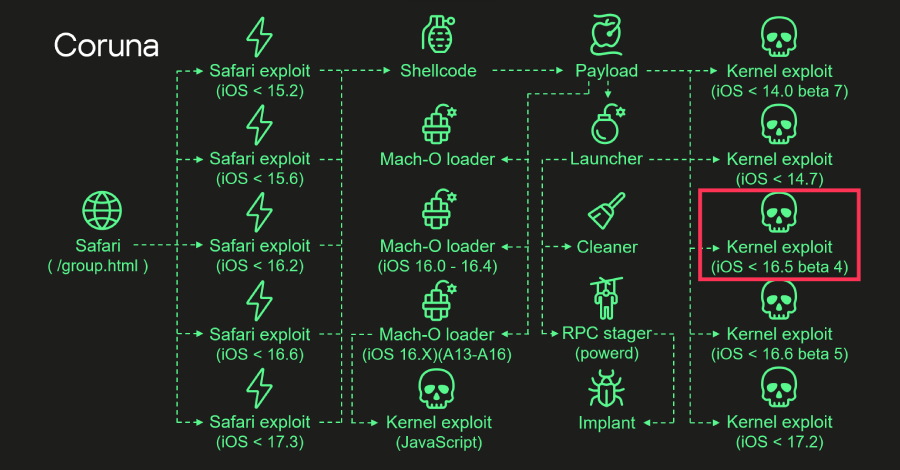
Ravie LakshmananMar 26, 2026Malware / Mobile Security The kernel exploit for two security […]